Gitlab Sast Template
Gitlab Sast Template - What is static application security testing (sast)? Stable vs latest sast templates sast provides two templates for incorporating security testing into your ci/cd pipelines: Gitlab advanced sast supports only modifying the. It automatically chooses which analyzers to run based on which programming languages are found in the. If you’re using gitlab ci/cd, you can use static application security testing (sast) to check your source code for known vulnerabilities. Sast, is a security technique designed to analyze an application’s source code, bytecode, or binaries for vulnerabilities. Replacing predefined rules by building a custom configuration using passthroughs. This guide describes how to start static application security testing (sast) in gitlab as efficiently as possible. This example shows how to run static application security testing (sast) on your project's source code by using gitlab ci/cd. To configure sast for a project you can: Wiz code can fill that gap. Configure sast using the ui (introduced in gitlab 13.3). Sast is a process where we use static code analysis to look for potential. If you’re using gitlab ci/cd, you can use static application security testing (sast) to check your source code for known vulnerabilities. This guide describes how to start static application security testing (sast) in gitlab as efficiently as possible. Sast, is a security technique designed to analyze an application’s source code, bytecode, or binaries for vulnerabilities. Stable vs latest sast templates sast provides two templates for incorporating security testing into your ci/cd pipelines: Replacing predefined rules by building a custom configuration using passthroughs. Static application security testing (sast) uses analyzers to detect vulnerabilities in source code. It automatically chooses which analyzers to run based on which programming languages are found in the. Static application security testing (sast) checks your source code for known vulnerabilities. What is static application security testing (sast)? Add sast_excluded_analyzers support in sast so that we can move away from sast_default_analyzers in the future Static application security testing (sast) uses analyzers to detect vulnerabilities in source code. If you’re using gitlab ci/cd, you can use static application security testing. To configure sast for a project you can: It automatically chooses which analyzers to run based on which programming languages are found in the. Static application security testing (sast) uses analyzers to detect vulnerabilities in source code. Replacing predefined rules by building a custom configuration using passthroughs. Wiz code can fill that gap. Sast, is a security technique designed to analyze an application’s source code, bytecode, or binaries for vulnerabilities. If you’re using gitlab ci/cd, you can use static application security testing (sast) to check your source code for known vulnerabilities. Configure sast using the ui (introduced in gitlab 13.3). Sast is a process where we use static code analysis to look for. What is static application security testing (sast)? Sast is a process where we use static code analysis to look for potential. This guide describes how to start static application security testing (sast) in gitlab as efficiently as possible. You can run sast analyzers in any gitlab tier. Sast, is a security technique designed to analyze an application’s source code, bytecode,. Use auto sast provided by auto devops. Static application security testing (sast) checks your source code for known vulnerabilities. Sast is a process where we use static code analysis to look for potential. Sast tools don’t cover iac templates, kubernetes configurations, or secrets detection—but these are critical in modern cloud environments. Replacing predefined rules by building a custom configuration using. Static application security testing (sast) uses analyzers to detect vulnerabilities in source code. Use auto sast provided by auto devops. Add sast_excluded_analyzers support in sast so that we can move away from sast_default_analyzers in the future If you’re using gitlab ci/cd, you can use static application security testing (sast) to check your source code for known vulnerabilities. Sast tools don’t. Wiz code can fill that gap. Gitlab advanced sast supports only modifying the. To configure sast for a project you can: Replacing predefined rules by building a custom configuration using passthroughs. What is static application security testing (sast)? Static application security testing (sast) checks your source code for known vulnerabilities. Use auto sast provided by auto devops. You can run sast analyzers in any gitlab tier. Static application security testing (sast) checks your source code for known vulnerabilities. Gitlab advanced sast supports only modifying the. Static application security testing (sast) checks your source code for known vulnerabilities. Add sast_excluded_analyzers support in sast so that we can move away from sast_default_analyzers in the future You can run sast analyzers in any gitlab tier. Stable vs latest sast templates sast provides two templates for incorporating security testing into your ci/cd pipelines: To configure sast for a project. Sast is a process where we use static code analysis to look for potential. Stable vs latest sast templates sast provides two templates for incorporating security testing into your ci/cd pipelines: If you’re using gitlab ci/cd, you can use static application security testing (sast) to check your source code for known vulnerabilities. You can run sast analyzers in any gitlab. Sast is a process where we use static code analysis to look for potential. To configure sast for a project you can: Sast, is a security technique designed to analyze an application’s source code, bytecode, or binaries for vulnerabilities. Gitlab advanced sast supports only modifying the. Use auto sast provided by auto devops. Stable vs latest sast templates sast provides two templates for incorporating security testing into your ci/cd pipelines: This guide describes how to start static application security testing (sast) in gitlab as efficiently as possible. Configure sast using the ui (introduced in gitlab 13.3). You can run sast analyzers in any gitlab tier. Static application security testing (sast) checks your source code for known vulnerabilities. What is static application security testing (sast)? Sast tools don’t cover iac templates, kubernetes configurations, or secrets detection—but these are critical in modern cloud environments. Wiz code can fill that gap. Gitlab sast uses a set of analyzers to scan code for potential vulnerabilities. Static application security testing (sast) checks your source code for known vulnerabilities. Replacing predefined rules by building a custom configuration using passthroughs.Integrating Fortify SAST into a GitLab CI/CD Pipeline YouTube
GitLab Buildin Templates GitLab SAST GitLab Tutorial YouTube
GitLab SAST Customize Rulesets Demo YouTube
Static Application Security Testing (SAST) GitLab
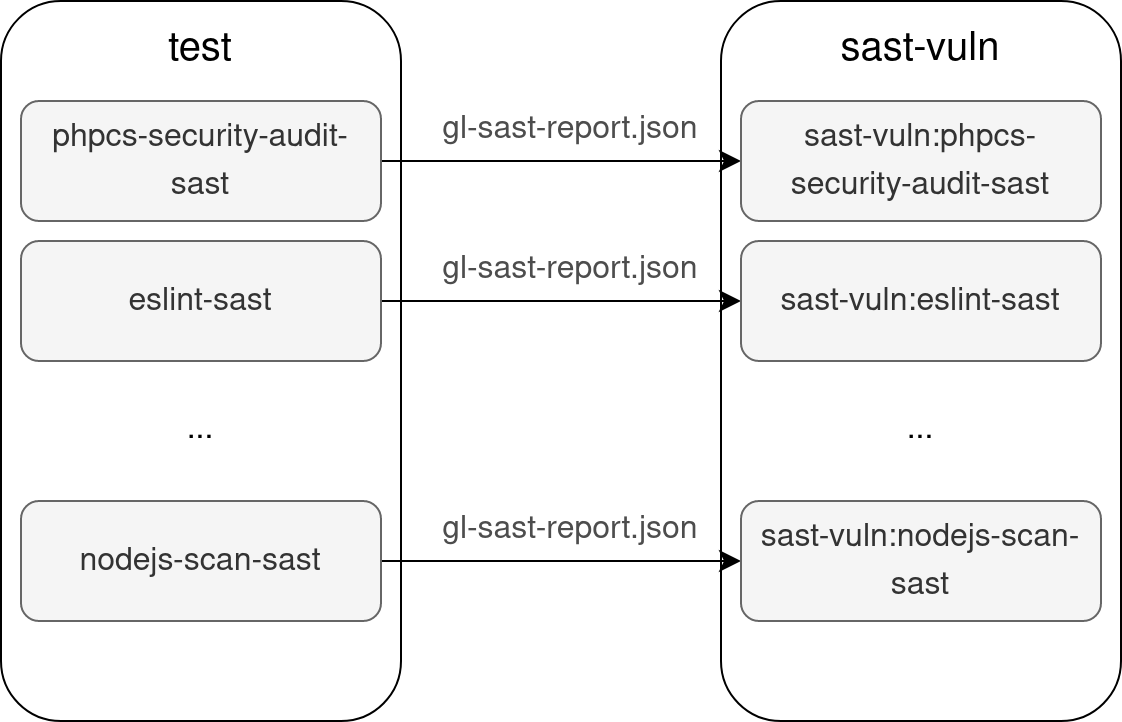
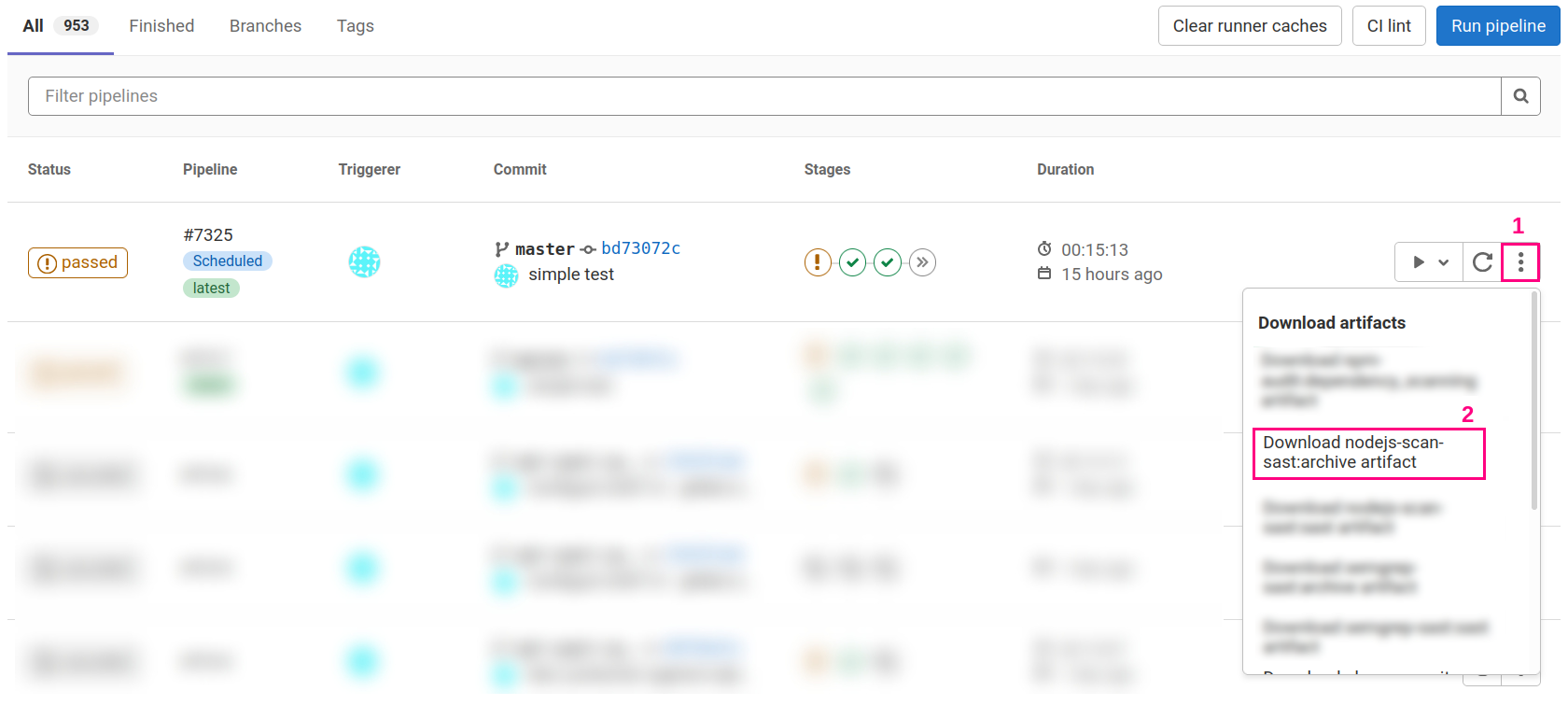
Secure your project with the GitLab SAST analyzers cylab.be
Secure your project with the GitLab SAST analyzers cylab.be
GitLab SAST How to Use GitLab With Klocwork Perforce
GitLab SAST How to Use GitLab With Klocwork Perforce
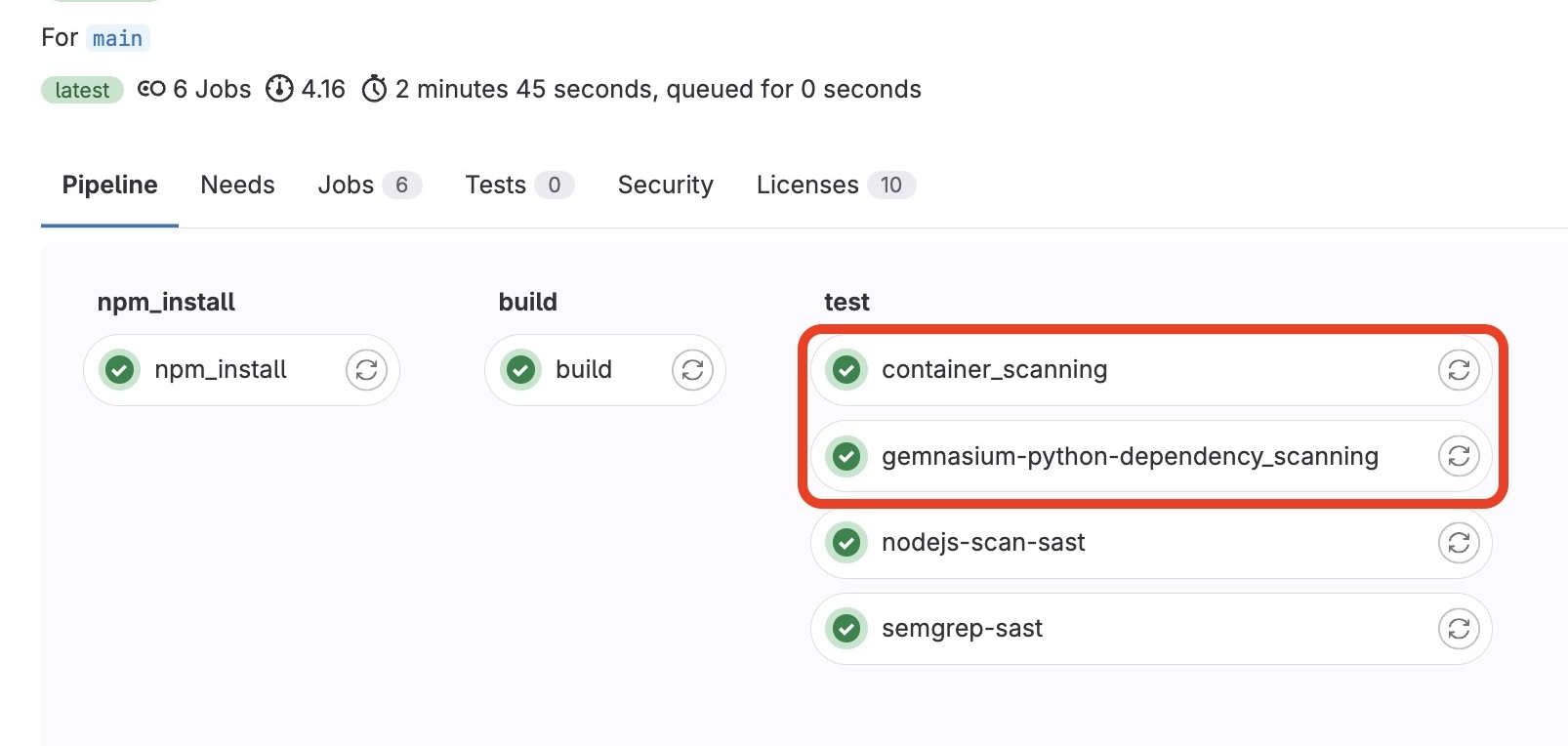
Elevating Container Security with Static Application Security Testing
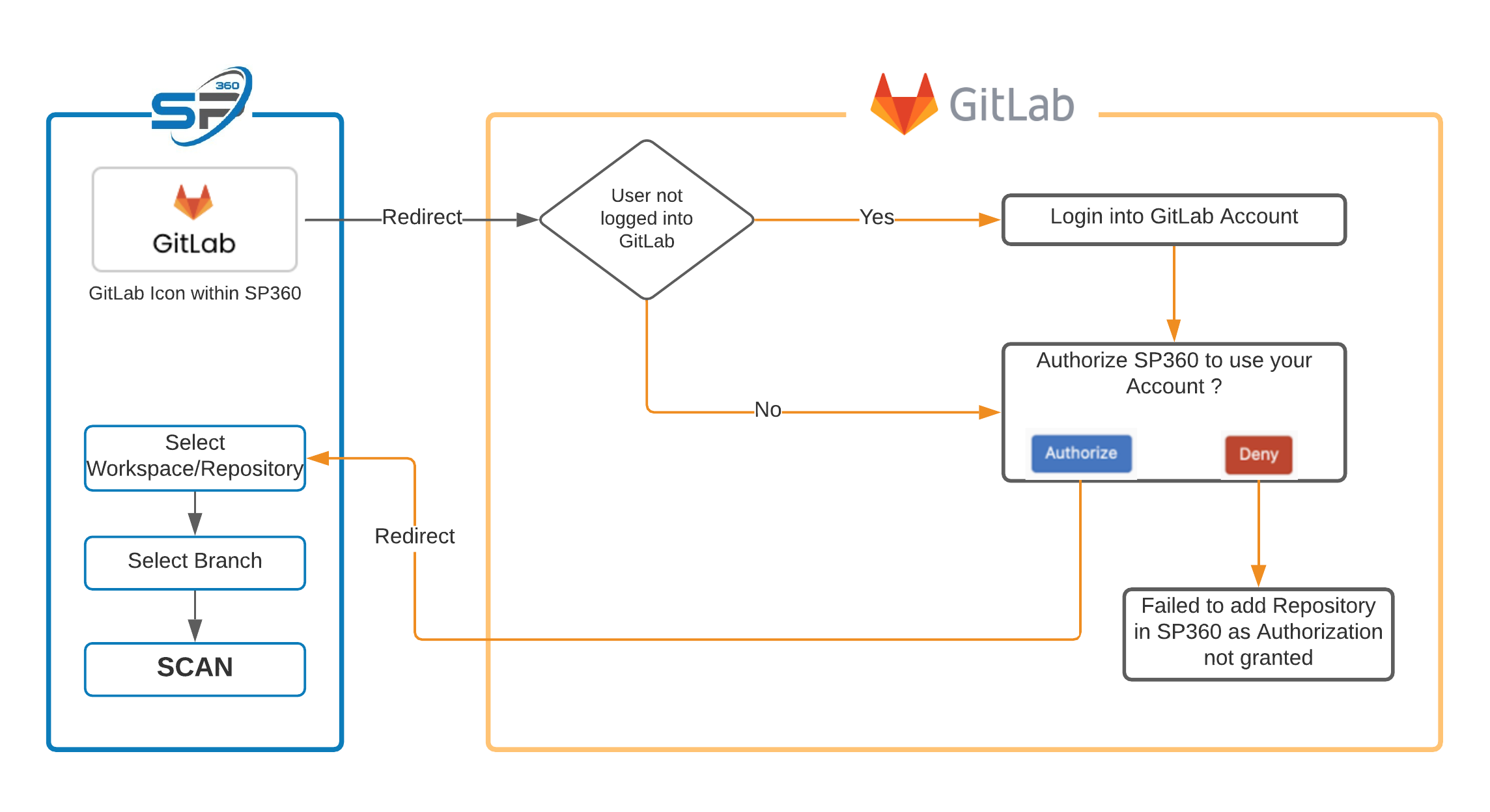
Sast gitlab SP360
Add Sast_Excluded_Analyzers Support In Sast So That We Can Move Away From Sast_Default_Analyzers In The Future
Static Application Security Testing (Sast) Uses Analyzers To Detect Vulnerabilities In Source Code.
This Example Shows How To Run Static Application Security Testing (Sast) On Your Project's Source Code By Using Gitlab Ci/Cd.
If You’re Using Gitlab Ci/Cd, You Can Use Static Application Security Testing (Sast) To Check Your Source Code For Known Vulnerabilities.
Related Post: