Information Technology Policy Templates
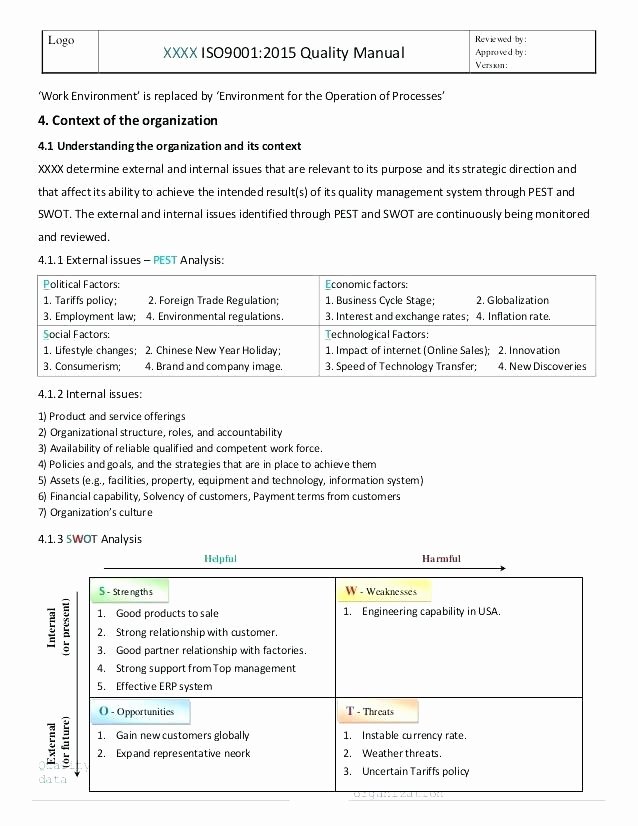
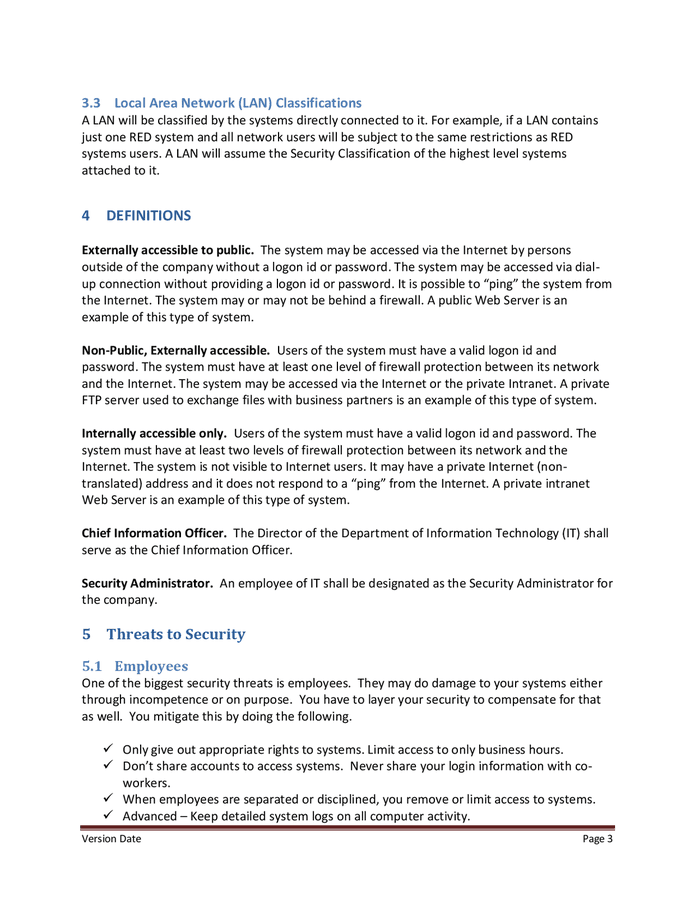
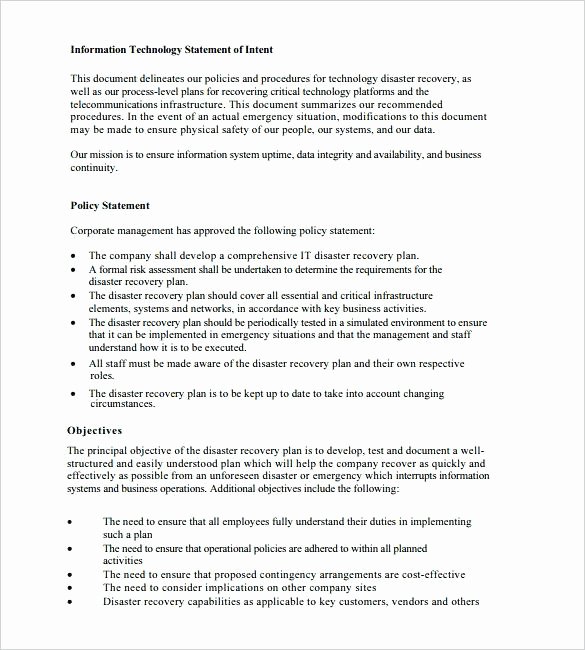
Information Technology Policy Templates - You can customize these if you wish, for example, by adding or removing topics. These are free to use and fully customizable to your company's it security practices. This document provides a template for an information technology (it) policy and procedures manual for small to medium sized businesses. Establish clear responsibilities for everyone involved in managing and protecting information, from the. Sans has developed a set of information security policy templates. Look no further than our comprehensive collection of it policies. The following templates are available as a guideline for agencies to develop their it security policies. Effective it security policy could be a model of the organization’s culture, during which rules and procedures are driven from its employees’ approach to their info and work. Hr resources tech & work internet and mobile phone reimbursement policy. If you have any kind of organization, then you might have to develop your own policies regarding how the organization operates. It includes sample policies and procedures on. Implement successful information technology governance strategies to reduce waste, enhance security, and align it initiatives with business goals. You can customize these if you wish, for example, by adding or removing topics. The following templates are available as a guideline for agencies to develop their it security policies. Below are the essential elements your policy template should include: Vita security baseline configurations (hardening standards) business impact. This template for an it policy and procedures manual is made up of example topics. Standards a standard is set of prescribed practices or. Are you looking to establish guidelines and regulations for your organization's information technology infrastructure? Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: You can customize these if you wish, for example, by adding or removing topics. It includes sample policies and procedures on. Explore the information technology policy and procedure templates available on way we do to add to your online standard operating procedures manual and add your own! This document provides a template for an information technology (it) policy and procedures. The following templates are available as a guideline for agencies to develop their it security policies. Processes and relationships that direct. For example, you would need to. Download sample information technology policy procedure template, designed to better your policies while simplifying it policy framework documentation. Effective it security policy could be a model of the organization’s culture, during which rules. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. These downloadable, customizable it policy, procedure, and documentation templates should be a part of every company’s operations manual. Download sample information technology policy procedure template, designed to better your policies while simplifying it policy framework documentation. Sans has. If you have any kind of organization, then you might have to develop your own policies regarding how the organization operates. These are free to use and fully customizable to your company's it security practices. For example, you would need to. The following templates are available as a guideline for agencies to develop their it security policies. Implement successful information. You can customize these if you wish, for example, by adding or removing topics. Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: These downloadable, customizable it policy, procedure, and documentation templates should be a part of every company’s operations manual. Processes and relationships that direct. Standards a standard. Establish clear responsibilities for everyone involved in managing and protecting information, from the. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Are you looking to establish guidelines and regulations for your organization's information technology infrastructure? Standards a standard is set of prescribed practices or. Our list. Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: These downloadable, customizable it policy, procedure, and documentation templates should be a part of every company’s operations manual. Due to the rise of the bring your own device movement, the lines have blurred between. Your it management should have all. This document provides a template for an information technology (it) policy and procedures manual for small to medium sized businesses. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Our list includes policy templates. Standards a standard is set of prescribed practices or. Sans has developed a. Implement successful information technology governance strategies to reduce waste, enhance security, and align it initiatives with business goals. Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: Processes and relationships that direct. The following templates are available as a guideline for agencies to develop their it security policies. Your. The following templates are available as a guideline for agencies to develop their it security policies. Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: This information technology (it) policy and procedure manual is for the small to medium sized business owner and their employees. These are free to. Why use a policy and procedure manual? Hr resources tech & work internet and mobile phone reimbursement policy. These are free to use and fully customizable to your company's it security practices. Implement successful information technology governance strategies to reduce waste, enhance security, and align it initiatives with business goals. The following templates are available as a guideline for agencies to develop their it security policies. Due to the rise of the bring your own device movement, the lines have blurred between. Below are the essential elements your policy template should include: Download sample information technology policy procedure template, designed to better your policies while simplifying it policy framework documentation. Learn how to write an information security policy, and download two templates on cybersecurity and network security perimeter policies to get started. Information technology cyber security policy 1 definition the use of the term “company” is in reverence to the following organization: This information technology (it) policy and procedure manual is for the small to medium sized business owner and their employees. Processes and relationships that direct. Vita security baseline configurations (hardening standards) business impact. If you have any kind of organization, then you might have to develop your own policies regarding how the organization operates. It includes sample policies and procedures on. Our list includes policy templates.Information Technology Policy Template
Information Technology Policy Templates
Information technology cyber security policy template in Word and Pdf
Information Technology Policies And Procedures Templates
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
Information Technology Policy Template
Information Technology Policy Template
Information Technology Policy Template Elegant Ict Security and Risk
42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab
Your It Management Should Have All These Policies And Procedures To Protect All Of Your Company Electronic Information And Critical Data.
This Template For An It Policy And Procedures Manual Is Made Up Of Example Topics.
Sans Has Developed A Set Of Information Security Policy Templates.
You Can Customize These If You Wish, For Example, By Adding Or Removing Topics.
Related Post:


![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-22.jpg)
![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-10.jpg)


![42 Information Security Policy Templates [Cyber Security] ᐅ TemplateLab](https://templatelab.com/wp-content/uploads/2018/05/Security-Policy-08.jpg)